There is a hard truth in web development that many SaaS founders learn too late: anything running in the browser is public. If your business model relies on hiding your frontend JavaScript logic behind obfuscation, you do not have a security strategy—you have a speed bump.
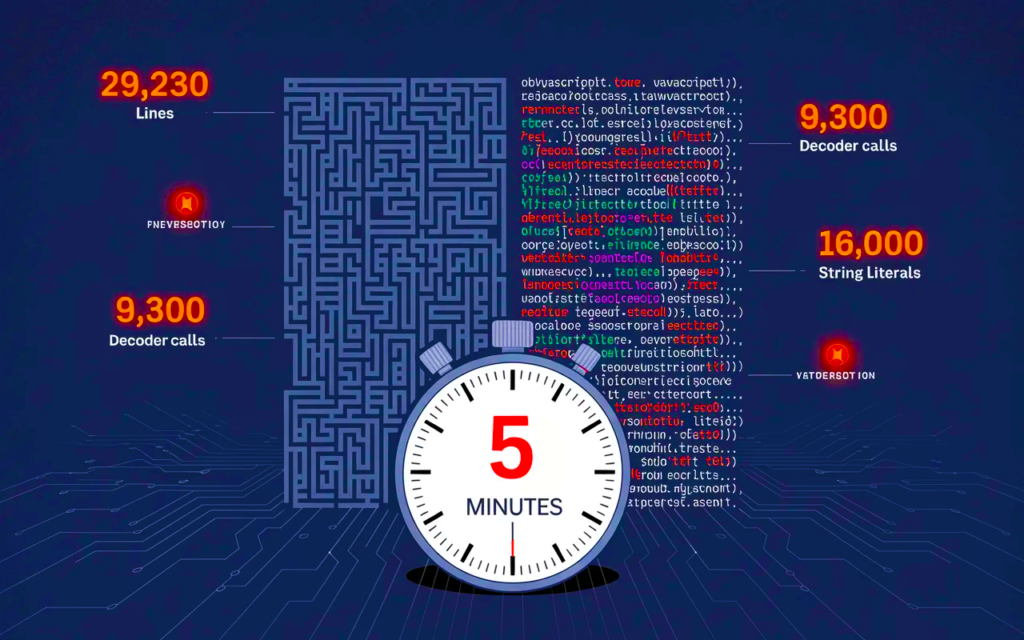
The 5-Minute Reversal
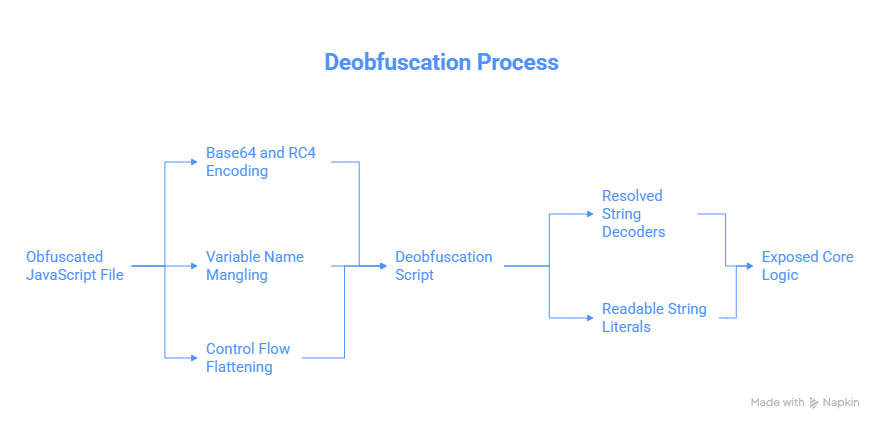
Consider a recent real-world test on a commercial web application. The target was a massive 29,230-line JavaScript file protected by industry-standard obfuscation techniques. It utilized:
- Base64 and RC4 string encoding.
- Variable name mangling.
- Control flow flattening and proxy wrappers.
To the naked eye, it looked impenetrable. In reality, it was completely deobfuscated in under five minutes using a 120-line Node.js script. The script automatically resolved over 9,300 opaque string decoder calls and revealed more than 16,000 readable string literals, exposing the core logic entirely.
The underlying mechanism is simple: the browser must execute the code. Therefore, the code must be readable to the machine. If the machine can decode it to run it, a human with the right tools can automate that exact same decoding process.
The Real SaaS Moat: Server-Side Architecture
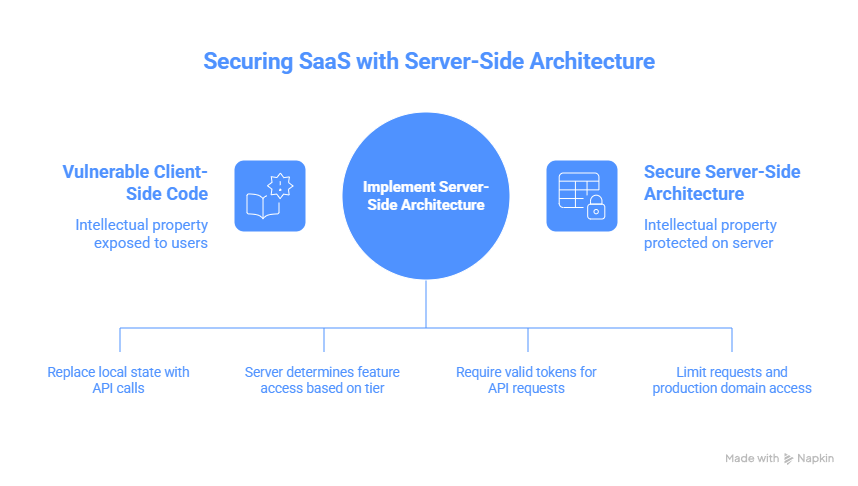
If client-side obfuscation is worthless, how do you protect your intellectual property? By moving the actual value to a place the user cannot reach.
Your competitive advantage must be your service, your data pipeline, and your backend execution—not your JavaScript. The frontend should merely be a “dumb client” that handles UI rendering and event capturing.
Here is what an actual security perimeter looks like:
- The API is the Authority: Replace local state management with authenticated API calls. If someone copies your frontend code, they should be left with a beautiful interface that cannot save, load, or process anything without valid server credentials.
- Server-Enforced Feature Gating: Never put subscription checks or trial limitations in JavaScript (e.g.,
if (trial)). The server must determine what data to return based on the user’s authenticated tier. - Short-Lived Tokens: Require valid session tokens (like JWTs) for every API request.
- Rate Limiting and CORS Lockdowns: Ensure your API only responds to requests from your production domain and limit request frequency to prevent abuse.
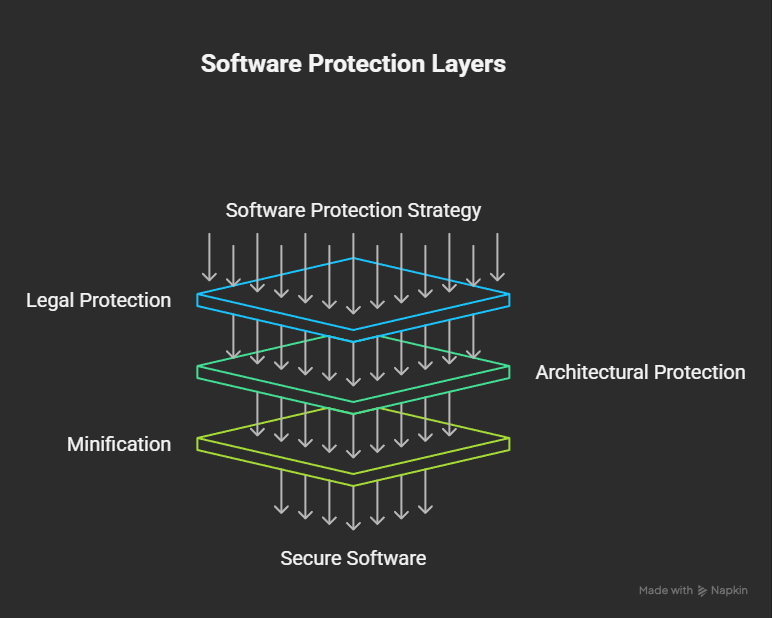
The Three Rings of Protection
Instead of wasting engineering cycles on theatrical obfuscation, structure your defenses functionally:
- Legal (The Outer Ring): Terms of Service, EULAs, Copyrights, and Trademarks. This is the only layer with actual enforcement power to deter legitimate competitors.
- Architecture (The Middle Ring): Server-side logic, authentication, and backend processing. This is technically impossible to bypass without compromising the server itself.
- Minification (The Inner Ring): Use standard minification tools for performance and load times, not security. Strip out source maps from your production builds and version-stamp your files. It makes casual reading harder without breaking your build pipeline.
At Axelar.eu, we know that true software protection isn’t about hiding code; it’s about building architectures where the client is disposable and the server is indispensable.